12.16.198.1100: System Traffic Analysis
The IP address 12.16.198.1100 plays a critical role in network traffic analysis. It provides a key reference point for monitoring data flow and identifying anomalies. Network administrators employ various methodologies to scrutinize this traffic. The analysis of patterns can reveal significant security vulnerabilities. Understanding these implications is essential for maintaining system integrity. However, the complexities of traffic behavior raise important questions about effective monitoring strategies.
Understanding IP Address 12.16.198.1100
The analysis of IP addresses is crucial for understanding network traffic and identifying potential security threats.
Examining the IP address 12.16.198.1100 reveals its role in network communication. This specific address may be associated with certain activities, necessitating scrutiny within network security frameworks.
Awareness of its implications aids in enhancing overall system integrity, promoting a secure and liberated digital environment for users.
Methodologies for System Traffic Analysis
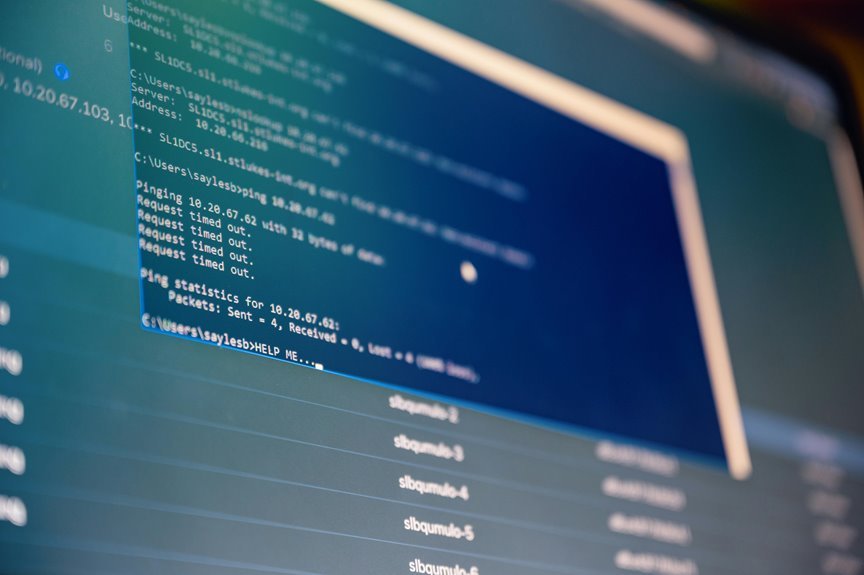
Various methodologies exist for conducting system traffic analysis, each offering unique advantages for monitoring and interpreting data flow within networks.
Techniques such as data visualization facilitate the representation of complex traffic patterns, while anomaly detection algorithms identify deviations from expected behaviors.
Together, these approaches empower network administrators to enhance security, optimize performance, and ensure the integrity of data transmissions across systems.
Insights and Implications of Traffic Patterns
Although traffic patterns can vary significantly across different networks, their analysis provides critical insights into system performance and security vulnerabilities.
Identifying traffic anomalies enables the detection of unusual user behavior, which may indicate potential threats or inefficiencies.
Understanding these patterns fosters informed decision-making, empowering network administrators to optimize resources and mitigate risks, ultimately enhancing the freedom and security of user experiences within the system.
Conclusion
In conclusion, the analysis of IP address 12.16.198.1100 reveals critical insights into network behavior, highlights potential vulnerabilities, and underscores the importance of proactive security measures. By employing advanced methodologies, such as anomaly detection and data visualization, administrators can not only identify deviations in traffic patterns but also enhance system integrity and promote a secure digital environment. Ultimately, this multifaceted approach ensures optimal performance, safeguards user safety, and fortifies the network against emerging threats.


