10.70.122.5589: System Address Analysis
The address “10.70.122.5589” exemplifies a critical issue in system address formatting. It exceeds the permissible limits of IPv4, which raises significant questions about its validity and potential impact on network performance. Misconfigured addresses can lead to vulnerabilities, affecting both security and resource allocation. Understanding the implications of such discrepancies is essential for maintaining a robust network infrastructure. What other factors contribute to effective address management in this context?
Understanding the Structure of System Addresses
The architecture of system addresses serves as a foundational element in computer networking and data management.
Understanding address formats is crucial, as they dictate how data packets are structured and routed. Effective address allocation ensures optimal utilization of network resources, facilitating seamless communication.
A well-defined address structure empowers users, enabling freedom in data management while maintaining the integrity and performance of the network infrastructure.
The Role of System Addresses in Network Management
While system addresses play a crucial role in network management, their significance extends beyond mere identification.
Effective address allocation enhances network performance by optimizing resource utilization and minimizing conflicts.
Additionally, well-structured addressing schemes enable seamless communication among devices, facilitating scalability and adaptability.
Thus, understanding and managing system addresses is essential for maintaining a resilient and efficient network infrastructure, empowering users with the freedom to innovate.
Security Implications of System Addresses
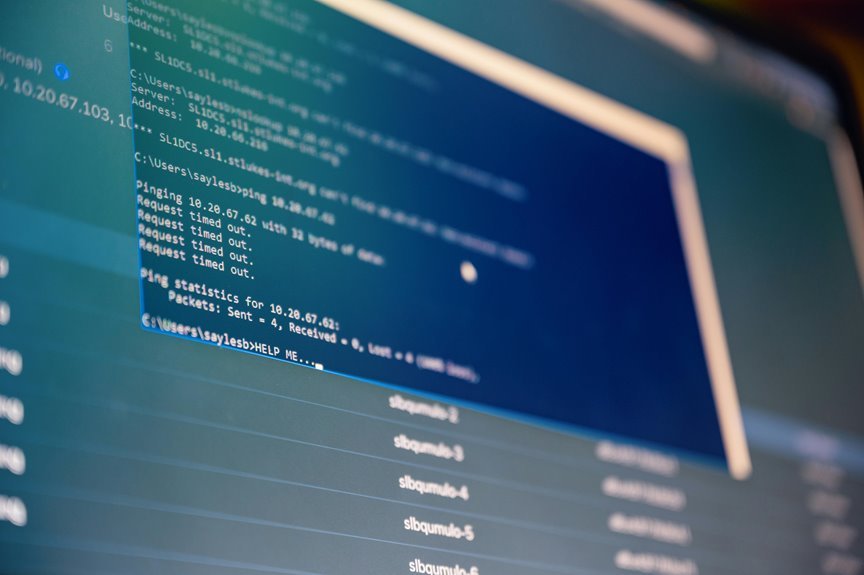
Understanding system addresses also reveals significant security implications that cannot be overlooked.
Address vulnerabilities threaten network integrity, as attackers can exploit these weaknesses to gain unauthorized access.
Additionally, address spoofing poses a serious risk, allowing malicious actors to impersonate legitimate systems.
Organizations must prioritize the identification and mitigation of these vulnerabilities to safeguard their networks and maintain the freedom and privacy of their users.
Conclusion
In the realm of digital communication, system addresses serve as the lifeblood of network connectivity, akin to the veins coursing through a living organism. However, the misstep of an incorrectly formatted address, like “10.70.122.5589,” illuminates the shadows of potential vulnerabilities lurking within a network. Vigilant analysis and meticulous management of these addresses not only safeguard against unauthorized incursions but also ensure an efficient, robust infrastructure, painting a secure picture of interconnectedness in an increasingly complex digital landscape.


