12.16.198.1100: System Traffic Analysis
The IP address 12.16.198.1100 is invalid, raising questions about its origin in network traffic analysis. Understanding the structure of valid IP addresses is crucial for effective system management. Traffic analysis techniques, such as packet capture, play a vital role in monitoring network behavior. These methods can uncover anomalies that may jeopardize security. As organizations seek to optimize performance, the implications of such findings warrant further examination.
Understanding IP Addresses and Their Role in Network Management
IP addresses serve as the fundamental building blocks of network management, enabling devices to communicate within a network.
There are various IP address types, including public, private, static, and dynamic, each serving specific functions.
Effective network segmentation utilizes these address types to enhance security and performance, allowing for organized data flow and improved resource management, ultimately fostering a more liberated and efficient digital environment.
Techniques for Analyzing System Traffic
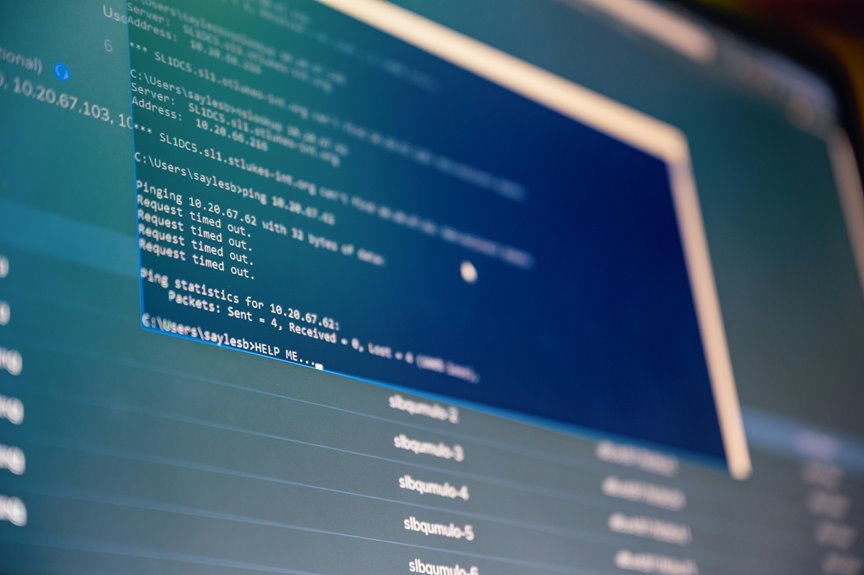
Analyzing system traffic requires the application of various techniques that can effectively identify patterns, anomalies, and performance metrics within a network.
Packet capture serves as a foundational method, enabling the collection of data packets for detailed examination. Coupled with traffic profiling, these techniques facilitate the categorization of network behavior, allowing for informed decision-making in optimizing performance and ensuring efficient resource allocation.
Identifying Anomalies and Enhancing Network Security
Effective identification of anomalies within system traffic is vital for enhancing network security.
Anomaly detection techniques, integrated into comprehensive network monitoring systems, enable the early recognition of irregular patterns that may indicate security breaches.
Conclusion
In the realm of network management, the invalidity of the IP address 12.16.198.1100 symbolizes the complexities and challenges inherent in system traffic analysis. Just as a distorted signal can obscure vital information, errant data points highlight the need for vigilant scrutiny and refined techniques. By illuminating anomalies and patterns, network administrators can forge a path toward enhanced security and optimized performance, transforming potential chaos into a coherent structure that supports the seamless flow of digital communication.


